Importance of Mobile App Security in Mobile App Development

Smartphones and tablets have been increasingly popular in recent years and a result there are many individuals and organizations that are developing mobile apps to make their business grow higher and their product constantly available to the users.
As per the recent data which reflect the pitiful condition of mobile application security, there are about 35% of companies that have never tested the mobile applications services they have created, and 40% of endeavors were found to not ensuring the clients they are producing for. It has also been seen that 11.6 million devices vulnerable to attacks, as per the recent reports of mobile application in security services.

If you are a business in the enterprise space and have not to deal with the mobile applications much, then you are likely not alarmed much by the headline “sure application security is important” but only for those businesses that are creating these mobile apps. Whether you build mobile apps for yourself, use them or consider them having someone to make one for you, understanding the mobile app security is the crucial key for each and every organization. All of the compliances of the mobile app make them vulnerable to security breaches.
The mobile app security basically defines the amount of protection an application on mobile devices has from the malware, phishing and other harmful hacker’s crime. People often try to install the apps from the sources which are not trusted or reliable that is pretty much invited for the malware into the device. This can also lead to a negative impact on other apps on your mobile phone because identity theft and financial hacks are becoming more and more common in today's economic scenario.
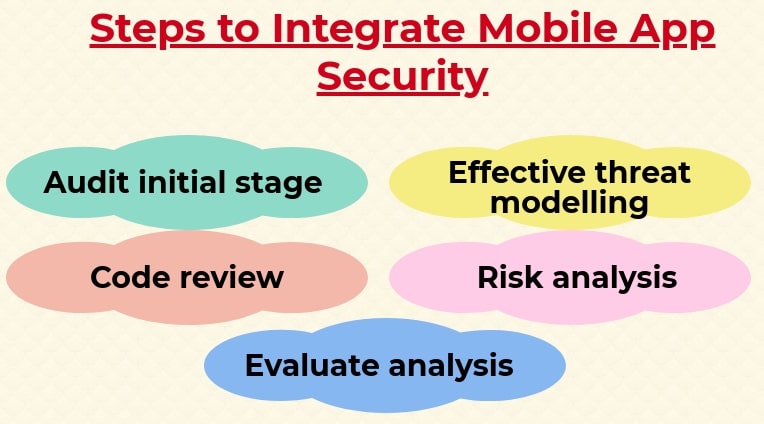
How to integrate mobile application security in mobile app development?
To integrate mobile application security in mobile app development, follow the given steps below:
-
Audit at the initial stage
To build up mobile application security, the security group should work with the application development group to look at the underlying dangers. This will also help to better comprehend the business coherence prerequisite for application security.
-
Effective threat modeling
In this phase, the security checking on the group must cooperate with the development group to pinpoint the zones in the application where delicate data is put anywhere. To accomplish the security of mobile apps, the developers need to perform risk demonstrating periods.
-
Code review
This is the step where the coding and development parts of the framework take place. Amid the development procedure, subsequent to testing is improved, important security testing for each audit unit ought’s to be directed and many more.
-
Risk analysis
For mobile application security, a quality check for any product is important before it ends up access to the client. The application ought to be completely tried with certain characterized parameters to diminish the dangers of a mobile app.
-
Evaluate risk
After the process of identification of basics required limiting dangers, it is important to rank, dissect and execute the fundamentals. For overseeing the methodology towards executing most reasonable basic ought to be made, the issues can be resolved rapidly for mobile apps security.
The need for mobile app security in mobile development
Let’s discuss the needs to address the mobile app security in the mobile app development process in effective manner:
-
Bring your hacked device
In the race to mobility and business costs, the businesses are rapidly warming up the idea of employees bringing their own devices to work on. Even the employees do not have an idea of how many ways the devices are being compromised. A recent report has reported that over 900 million Android devices can be fooled into giving root access to the malicious apps.
-
Security networks
It is not just your office premise where security compliances are made each day. With the help of personal devices, the employees can go home and plug into their other devices and networks By acknowledging the importance of mobile app security, you are avoiding putting much more on the line than you would otherwise.

-
Fight fire with fire
If threat intelligence was only the part of solution and humans were able to find out their way around it, then why not to create the solution with the combination of both to ensure maximum security? This will bring use what experts call threat hunting. The business using threat hunting as a part of security strategy has experienced a downfall in successful breaches
-
Threat intelligence
Threat intelligence is the new talk of the town which is basically a solution that experts believe can warm the business of possible plotted attacks by adopting the proactive stance with constant monitoring of activities both on networks and externally. Business has been doing this type of monitoring for some time and makes it error free.
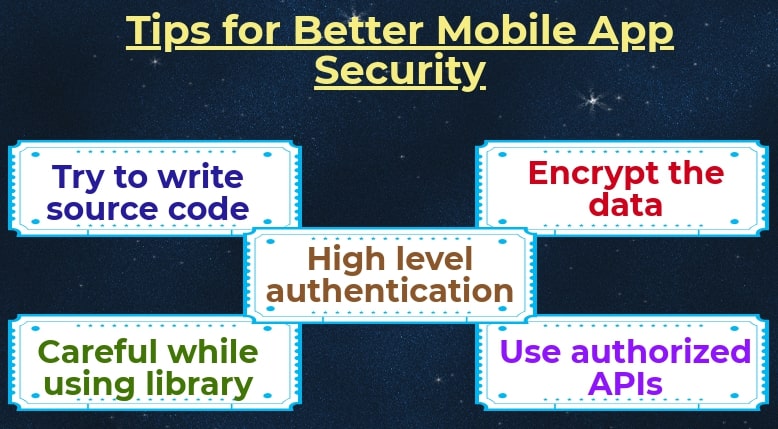
Tips for better mobile application security
Here are some of the common ways by which you can build completely safe and secure mobile apps for your organization as:
-
Try to write secure code
The code is the most vulnerable feature of any mobile application that can be exploited easily by hackers. Hence, it is quite important that you should write a highly secured code for your apps. As the research reports, about 11.6 million devices are usually affected by the malicious code issue. The best practice to develop best quality code is cord hardening and signing.
-
Encrypt the data
Encryption is the common way to convert the data transmitting into such form which cannot be read by anyone else without encryption. This is the major and most effective manner to save the data from being used in a malicious way. Therefore, even if the data is stolen, the hackers cannot decrypt it and it is of no use for them too.
-
Careful while using libraries
Oftentimes, the mobile app code requires third-party libraries for the code building process. Therefore, you should not trust the library for your app building as most of them are not secured. When you have used various types of libraries in it, then you should always try to test the code. The flaws in the library can help you to crash the system and not to use malicious code.
-
Use authorized API
You should always remember to use authorized APIs in your app code and it always gives the hackers the privilege to use your information. Authorization information caches can be used by hackers to gain authentication on the entire system. Therefore, experts recommend having central authorization for the whole API to gain maximum security in a mobile application development system.
-
Use high-level authentication
Authentication mechanism is the most significant part of mobile application security. Weak authentication process is one of the top vulnerabilities in mobile apps. As the developer a user authentication it should be considered important from the security point of view. One of the most common modes of authentication is through password which cannot be broken by hackers easily.
[Also Read- Top 10 trends in Mobile Application Development]
Conclusion
In the near future, security will act as one of the best differentiator, and competing for innovation in the mobile application services with the customers preferring secure apps to maintain the privacy of their data over other mobile applications.
Recent Blog

Why Your Business Needs a Mobile App?
06-Dec-2022Related Blogs



A secret of Mobile Application Development
23-Apr-2018
Market Demand for CRM and ERP Development
07-May-2018










